All Stories
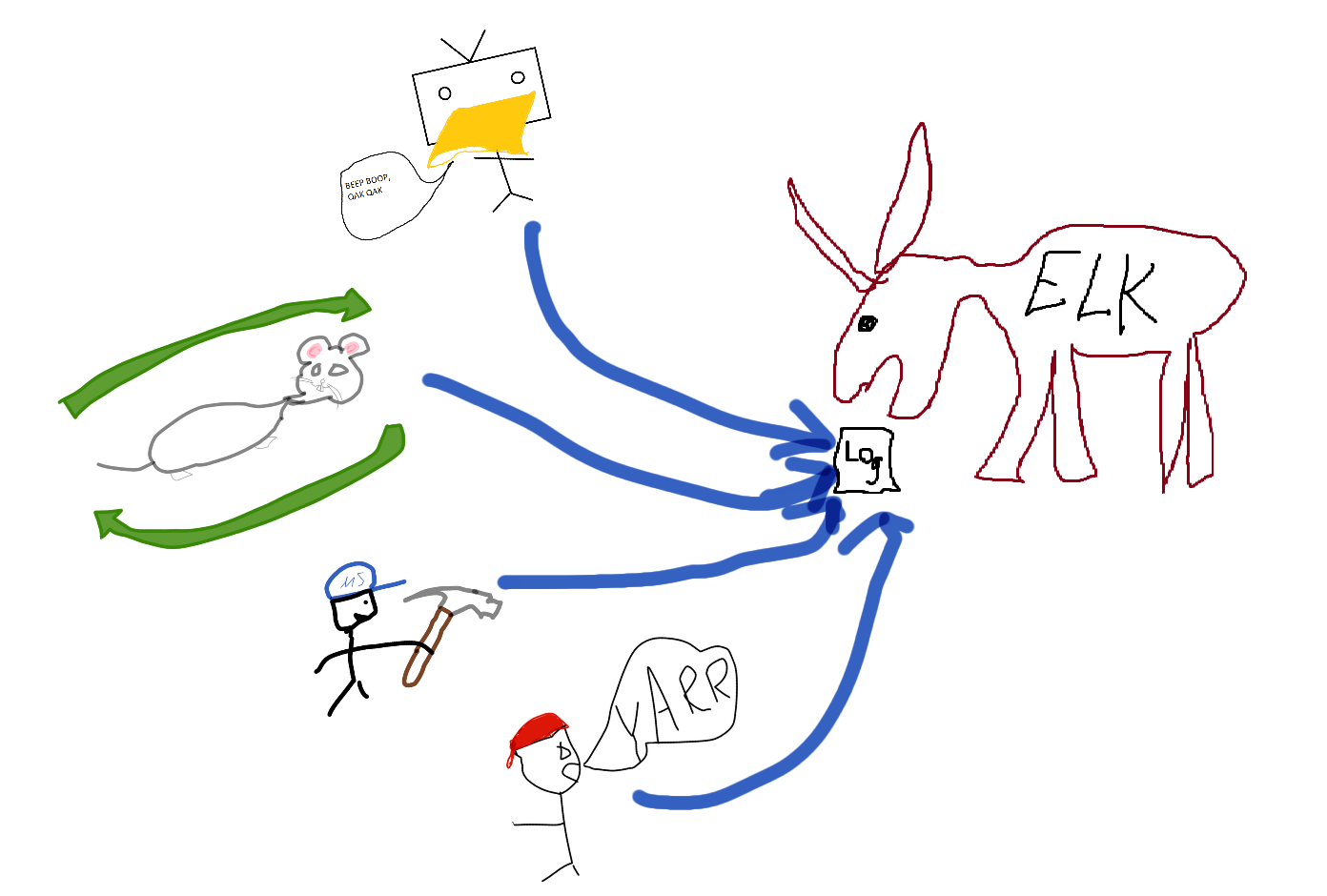
Malware statistics to ELK
I’ve been somewhat busy lately and hadn’t had much time to write anything to the blog unfortunately. I also have had some issues in thinking of good topics as I don’t want to get stuc...
In threat hunting, Feb 16, 2023MDE/MDI/MDO365 advanced hunt queries to ELK
I’ve been using Jupyter Notebook for quite sometime in threat hunting and incident response purposes. It is great as it offers the python data analytic tools to be used with the data ...
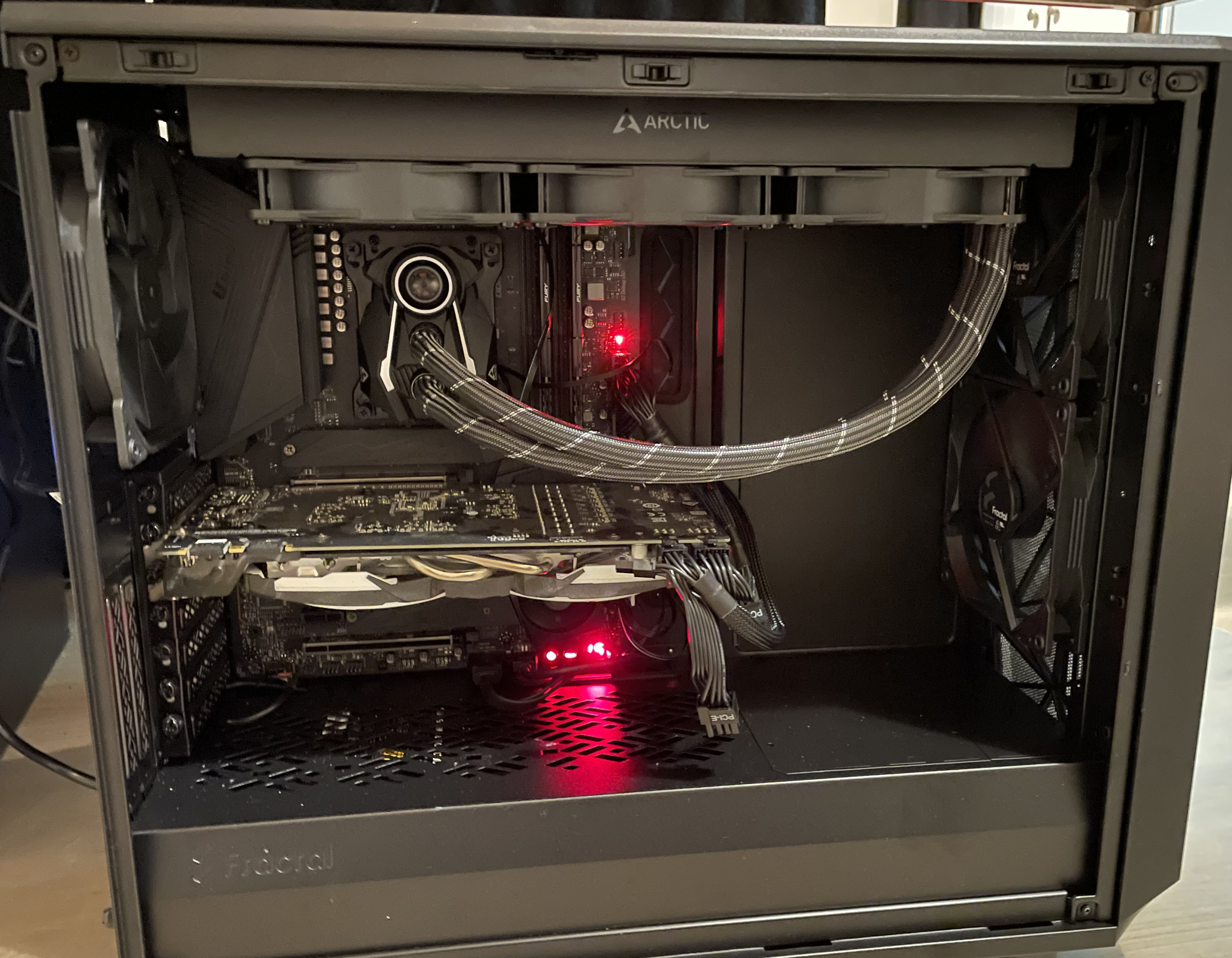
In threat hunting, Nov 28, 2022My version of a home lab
This time I am going to introduced my version of a home lab. This is not as “pro” as many others have but have a good combination of lab and a home computer in a same package. The pos...
In threat hunting, Nov 19, 2022Recent phishing emails + Emotet recent sample analysis
Phishing emails
In threat hunting, Nov 13, 2022Featured
-
Machine Learning for Threat Hunting
In Threat Hunting, -
Autonomous SOC, part 2, isolating agent
In SOC, -
Autonomous SOC, possible or just pointless AI hype?
In SOC, -
Why Your Threat Hunting Program Is Working (Even When It Finds Nothing)
In threat hunting, -
OpenCTI RSS feed support
In threat intelligence, -
Threat Intelligence Platform - OpenCTI
In threat intelligence,